Third-Party Risk Management Software
Riskonnect’s Third-Party Risk Management software consolidates all vendor and supplier information to minimize your exposure and maximize your benefits throughout the entire relationship.
Choose vendors with confidence. Know the facts about a vendor’s security status, financial strength, and level of risk before onboarding them to your company.
Build third-party relationships based on trust. Engage your partners in frank, productive conversations around your standards and expectations.
Keep important documentation ready-to-go. Rest assured that documentation and data are always updated and available when you need it.

Third-Party Risk Management Software
Product Highlights
Because of Riskonnect, we were able to move forward with a new piece of business. We were able to expand operations team revenue growth – and increase vendor compliance. Onboarding is a very seamless process for our team and for our vendors.”
Workers’ Compensation Manager, Stanley Steemer
Free Up Time for
More Important Things
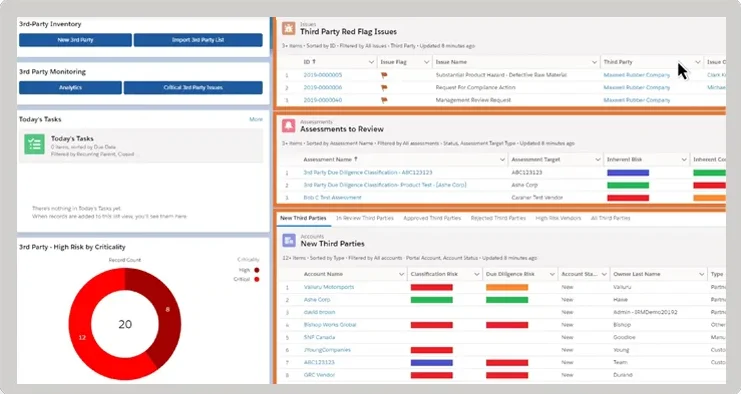
How can you understand your level of vendor risk if you spend all day sending and coding assessments? Riskonnect’s Third-Party Risk Management software is designed to take manual tasks off your plate, so you can focus your time on more important things like building relationships.
- Automate workflows to save time and improve reliability.
- Quickly onboard new vendors.
- Turn around supplier assessments much faster, at a lower cost.
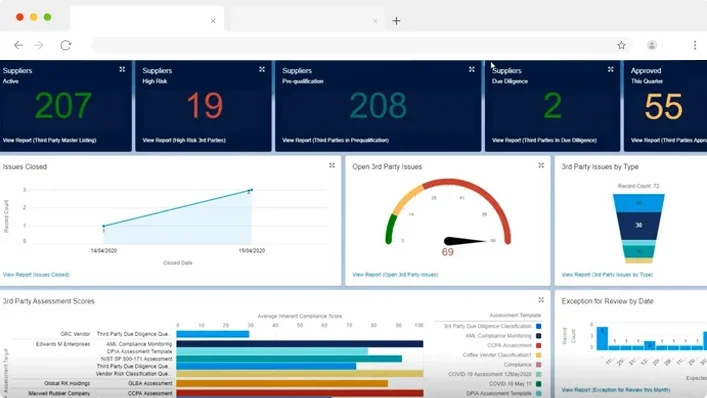
- Easily communicate vendor risk profiles with clear, real-time reporting.
- Better prepare for third-party churn and offboarding.
Increase
Visibility to Risk
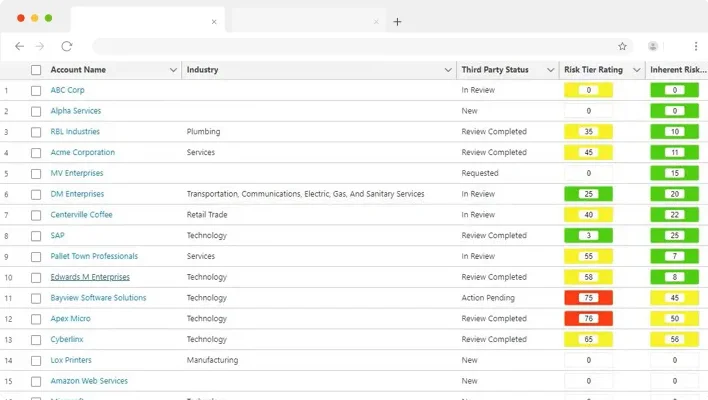
How can you build a clear picture of third-party risk when assessments and documentation are inconsistent or missing? Riskonnect’s Third-Party Risk Management software gives you the ability to track relationships from beginning to end, giving you instant insights to understand the full story.
- Get agreements, contracts, policies, and credentials all in one place.
- Calculate risk scores for each supplier and automatically set reassessments.
- Be audit-ready with easy-to-access third-party documentation.
- Elevate your assessments with insight into your suppliers’ risk.
Build Trusting
Relationships
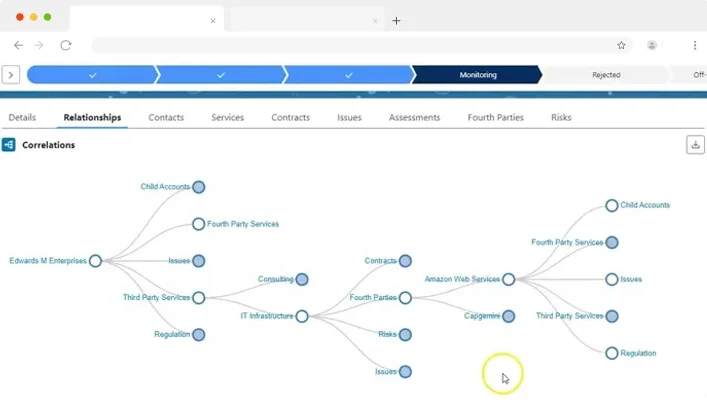
How well do you know and trust your vendors? Riskonnect’s Third-Party Risk Management software helps you establish strong, two-way communication with your vendors to build successful relationships based on mutual respect and a shared purpose.
- Make fact-finding easy with consistent, coordinated supplier assessments.
- Chat with suppliers in-app to get answers and check status.
- Gain the appreciation of suppliers with our easy-to-use portal for submitting documentation.
Tell Your Story
with Confidence
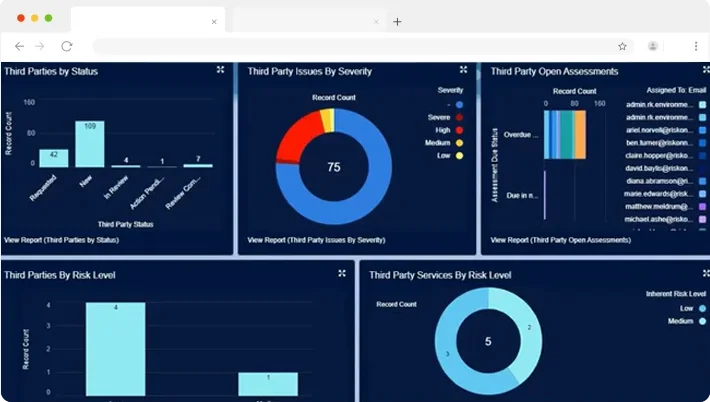
How can you build a clear picture of third-party risk when assessments and documentation are inconsistent or missing? Riskonnect’s Third-Party Risk Management software gives you the ability to track relationships from beginning to end, giving you instant insights to understand the full story.
- Get agreements, contracts, policies, and credentials all in one place.
- Calculate risk scores for each supplier and automatically set reassessments.
- Be audit-ready with easy-to-access third-party documentation.
- Elevate your assessments with insight into your suppliers’ risk.
Get Started with These Helpful Resources
Industry Recognition for Riskonnect