Threat Intelligence Software
Riskonnect’s Threat Intelligence software helps you monitor global threats in real time and respond faster and more effectively to critical events.
Boost situational awareness. Understand the real-time context of events that could affect your organization so you can move faster to secure your people and assets.
Filter out the noise. Easily customize the geographies, threat types, and severity levels to stay focused on only the events that are relevant to your organization.
Act faster with automation. Configure automatic alerts and system workflows to be triggered when specific threat conditions occur, saving time and expediting your response.
Threat Intelligence Software
Product Highlights
Riskonnect is so easy to understand, and the mobile app and single sign-on capabilities offer a huge advantage. When everything is hitting the fan, the last thing you want to do is wrestle with your system. Even if the power is out, we still have the plans in our pockets.”
Doug Fleming, Senior Director of Environmental, Health, Safety, Business Continuity, and Sustainability, Bio-Rad
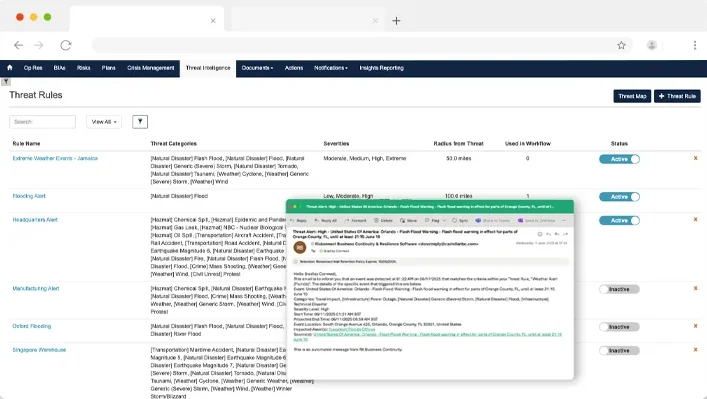
Initiate Your
Response Automatically
How much time do you waste getting your act together before you can respond to a disruption? Riskonnect’s Threat Intelligence software allows you to respond immediately with automated strategic workflows and alerts.
- Build workflows that instantly alert stakeholders or response teams when a threat meets your specific criteria.
- Take immediate action after reviewing a threat – like creating a new incident or sending mass notification – using the on-page actions menu.
- Easily configure rules around who should be alerted and when.
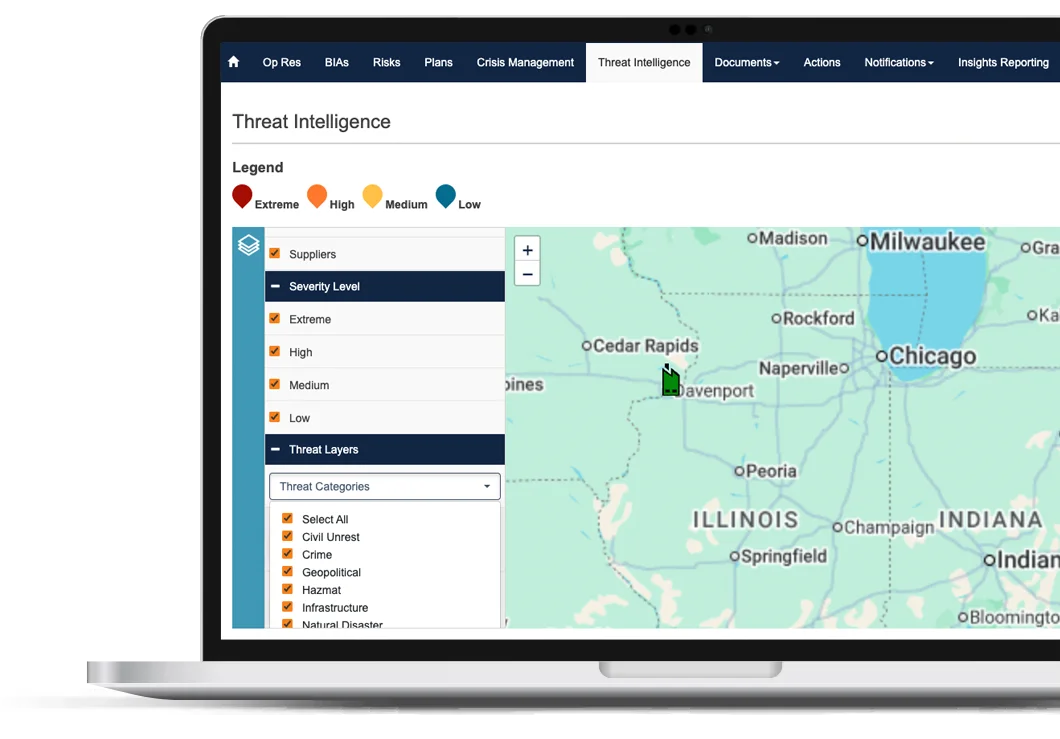
Continuously Monitor
Your Most Critical Assets
Are you confident that the assets most critical to your organization’s operations are secure at all times? Riskonnect’s Threat Intelligence software allows you to keep tabs on everything happening around your assets to maintain business continuity.
- Select the most important internal contacts, suppliers, and locations to monitor on the threat map.
- Evaluate threats by low, medium, high, and extreme severity levels, and set a monitor radius from each location.
- Manually create your own threat event to record disruptions unique to your business or processes.
Maintain Real-Time
Awareness Using a Single Solution
Are you overloaded with information from various sources through different channels? Riskonnect’s Threat Intelligence software provides a comprehensive view of your risk landscape in one place, giving you a better understanding of which disruptions are actual threats to your operations.
- Pull in information from global data sources like news (local, national, and international), federal government agencies, curated social media feeds, and more.
- Use a single viewpoint to see all threat categories, ranging from natural disaster to civil unrest and crime.
- Manage all readiness and response activities in one platform to centralize your operations and reduce manual workload.
Get Started with These Helpful Resources
Industry Recognition for Riskonnect


Your Threat Intelligence Software Questions Answered




